Security researchers have spotted a spearphishing campaign that targets companies in the oil and gas sector to drop Agent Tesla malware.
Researchers from Bitdefender say the bad actors are impersonating an engineering contractor in Egypt (Enppi – Engineering for Petroleum and Process Industries) to target multiple energy companies. Those victims include organizations in Malaysia, the United States, Iran, South Africa, Oman, Turkey and other countries.
In the midst of the global COVID-19 pandemic, the oil and gas industry has been under enormous strain. Oil prices per barrel dropped to the lowest prices since 2002 as demand has cratered.
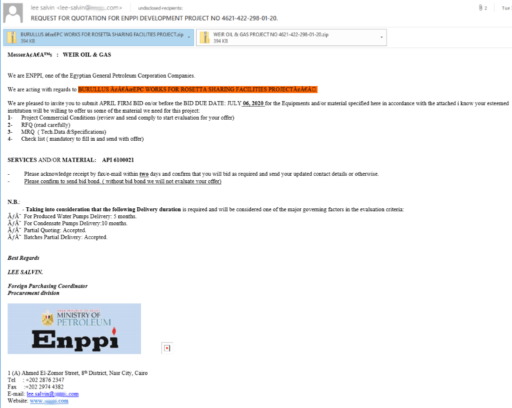
Bitdefender warns the spearphishing email is well crafted and targeted:
“The spearphishing email mimics Egyptian state oil company Engineering for Petroleum and Process Industries (Enppi) and claims to invite the recipient to submit a bid for equipment and materials, as part of a project (Rosetta Sharing Facilities Project) on behalf of a well-known gas company (Burullus).”
Bitdefender
Furthermore, the email request to submit a bid includes an attachment that contains a “list of requested materials and equipment.” The infected file is used to drop the Agent Tesla spyware Trojan. See Figure 1 below:
Actors use Agent Tesla malware to collect sensitive information and steal credentials.
Bitdefender said the cyber attacks spiked on March 31 and were “well orchestrated” based on its relatively low volume and targeted towards oil and gas sector.
The experts also warn that attackers “also target other energy verticals that have been tagged as critical during this Coronavirus pandemic.”
Cisco’s Talos security group discovered Agent Tesla back in October of 2018. The company confirmed the malware at that time could steal user’s login information from multiple software, to include Google Chrome, Mozilla Firefox, Microsoft Outlook and others.
